Integrated digital production footprint, unsecured data centers hosting data from multiple technology streams such as IoT, OT and IT, and rapid ingress of new and emerging tech are creating new vulnerabilities that are persistent and disruptive.
Consider these scenarios:
- A connected component within a network can give cyber criminals access to a larger network. A single vulnerability can thus serve as a beachhead for a multitude of attacks.
- Distracted employees may unintentionally download malware, leave ports open or ignore signs of a data breach.
- The addition of new and untested components could create new vulnerabilities as these could be pre-rigged with trojans.
- Cybersecurity teams are struggling to handle an explosion of attack surfaces in the aftermath of the ongoing pandemic.
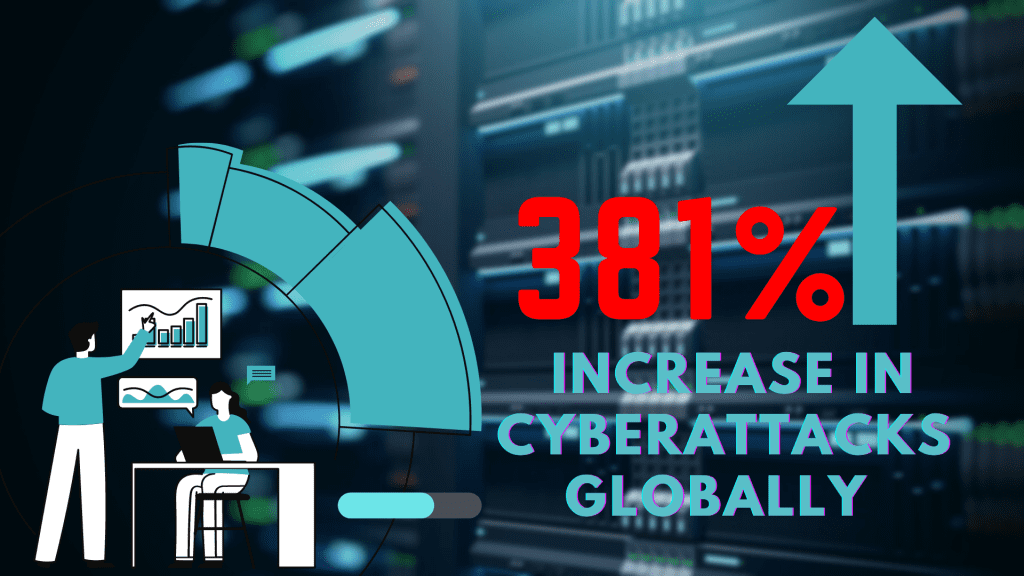
In the first three months of 2021, cyberattacks have grown by 381 percent globally. Such attacks have been facilitated by data stolen and transferred in 2020 and unfixed vulnerabilities. This is according to our threat research team. Learn more about the research on The Global Threat Landscape Report .
Subex Secure is a specialist in protecting your IoT and OT infrastructure from cyberattacks. Our cybersecurity solution Subex Secure protects infrastructure, assets, data, and networks. It is a three-tier threat detection feature that identifies and flags threats early preventing lateral movement of malware. It can also discover rogue devices and mitigate threats.
Talk to us about improving your cybersecurity posture and eliminate cyberthreats immediately.