Now that cybercrime is becoming more advanced, how can cybersecurity protocols evolve to keep fighting against cyber theft? The National Institute of Standards and Technology’s (NIST) Cybersecurity Framework or CSF was created to help businesses combat cybercrime by providing a standard that they can follow to keep their online resources protected. Even now, the NIST is constantly updating its procedures. Such updates include the release of the NIST SP 800-53A revision, which provides a methodology to ensure and verify that the security and privacy outcomes of organizations are being achieved.
Table of Contents
These updates are driven by the persistence and evolution of cyber attacks. A write-up on the cybersecurity skills gap by Maryville University notes how businesses are set to lose $8 trillion to cybercrime over the next five years – and very likely more – as we grow increasingly connected in the digital realm. Inadequate cybersecurity coupled with increased internet connectivity heightens the chances of a cyberattack, putting valuable information at risk of falling into the wrong hands. Though the NIST framework is voluntary, businesses should consider adopting the CSF as a structure to figure out cybersecurity measures that suit and serve the organization well. The framework can be tricky to comprehend, so we’ll break its main parts down to make things easier.
Understanding NIST CSF
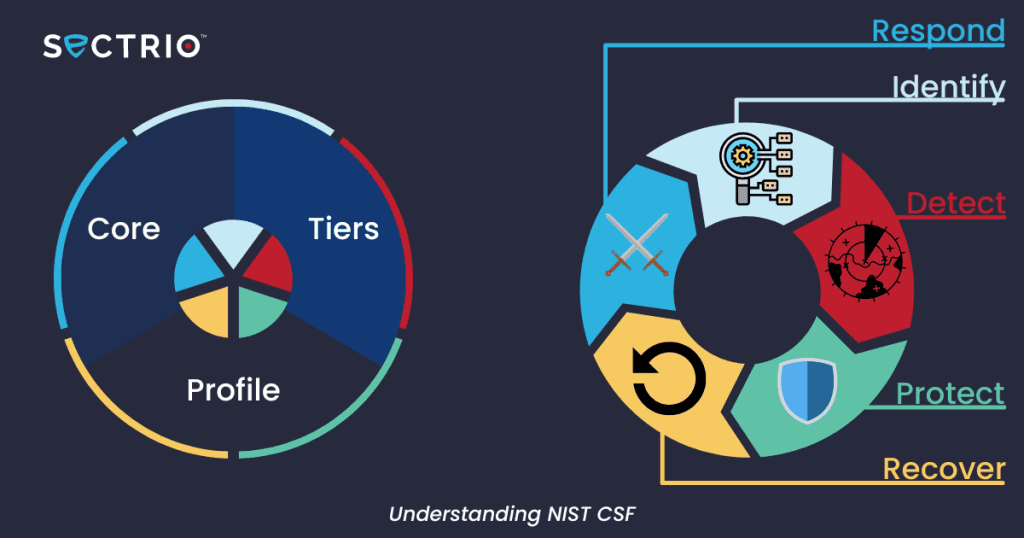
The CSF consists of the core, tiers, and profile, aligning cybersecurity activities with your business’s resources and requirements.
The Core
The core is a set of cybersecurity activities, outcomes, and references to achieve those outcomes. It provides standards, guides, and practices that can be communicated and adopted at all levels of the business. The core’s functions organize basic cybersecurity measures and provide tasks to manage incidents. These are:
- Identify: Take note of your assets such as your equipment, systems, software, and data.
- Protect: Back up and encrypt data regularly, as well as limit access and control to it. Use security software to keep your systems protected. Train employees on cybersecurity and walk them through any security measures and protocols before, during, and after a cyberattack.
- Detect: Monitor activity regularly to quickly and easily point out anything suspicious or unauthorized and manage the potential threat.
- Respond: Have a clear response plan and frequently communicate with those involved in containing the attack. Be transparent about whose data is at risk and notify them immediately. Make changes to weak points in the plan and test new efforts to make policy improvements that can provide better protection in the future.
- Recover: Address the affected equipment or information and have it repaired or restored to the best of your capabilities. Update all parties on the event and the changes to protocols, and work together to improve security.
Within these functions are categories containing specific tasks that need to be accomplished, such as “asset management” and “risk assessment.” Categories are further divided into sub-categories with more particular tasks. Informative references are guidelines and practices to be followed to achieve the outcomes under the sub-categories.
Tiers
https://www.youtube.com/embed/UfViT53WUR0?feature=oembedOverview of NIST Cybersecurity Implementation Tiers
The implementation tiers assess the company’s cybersecurity measures and processes, how well they work and if they adhere to the CSF standards. They range from tier one to four:
- Tier One (Partial): Cybersecurity protocols are informal and inconsistent.
- Tier Two (Risk-informed): The business is aware of risks and has more cybersecurity measures, but there are no organization-wide policies.
- Tier Three (Repeatable): Risk management policies are formal and company-wide; they consistently provide sufficient protection.
- Tier Four (Adaptive): The business completely adopted the CSF. Threat detection is proactive and evolving.
Knowing which tier your business falls under can help you improve to reach the next tier and eventually achieve more efficient, proactive cybersecurity.
Profiles
Framework profiles describe the current or desired state of the organization’s cybersecurity protocols. The Current Profile details the business’s cybersecurity outcomes that are presently being achieved. The Target Profile lays out the outcomes that need to be completed to get to the desired cybersecurity management goals. Comparing the two can help address the gaps and areas for improvement to reach the Target Profile.
As noted by Virginia Tech, cybercrimes are constantly evolving and not limited to attacks on individuals but on institutions as well. The CSF may be optional, but its standards and practices are essential in protecting your business and its information in the digital age. For more information about the NIST and its revisions, you can check out our post on possible CSF updates.
Want to learn more about OT security? Talk to an OT cybersecurity expert from your industry now.
We are giving away threat intelligence for free for the next 2 weeks. Find out how you can sign up and try out our threat intelligence feeds

Simplifying NIST Cybersecurity Standards & Framework – Sectrio
Find out what is lurking in your network. Go for a comprehensive 3-layer threat assessment now
Join our Cybersecurity Awareness Month campaign
See our solution in action through a free demo





