Between cyber-criminal groups, Lazarus (North Korea), Conti (Russia), and Mustang Panda (China), almost every business in every sector is on the radar of hackers. Because of geopolitical and economic reasons, these groups have stepped up their scanning and target acquisition activities in the last 4 weeks. Though evidence of collaboration is scant, there is some evidence to indicate that at least two of these groups have exchanged a list of targets in the past.
So what have we got to worry about?
- Targeted attacks on OT networks are rising and depending on who is attacking, the motivation could be anything from ransom, disruption, elimination of competition, or even training
- Oil and gas facilities have been successfully targeted in the last two months and the ransom that came from these attacks has fueled a new wave of attacks by Conti (including the launch of a new multi-loader malware that was released early)
- While Lazarus is primarily targeting the financial services sector, it could switch to attacking manufacturing units and other critical or large chemical processing units for ransom
- Most attacks are based on spear-phishing using specific messaging
- By targeting oil and gas and manufacturing, the hackers are also trying to destabilize economies and large supply chains
- Even without these events, 2022 has been a tough year for CISOs with
Cyber threat assessment for IT, OT, and IoT is the need of the hour
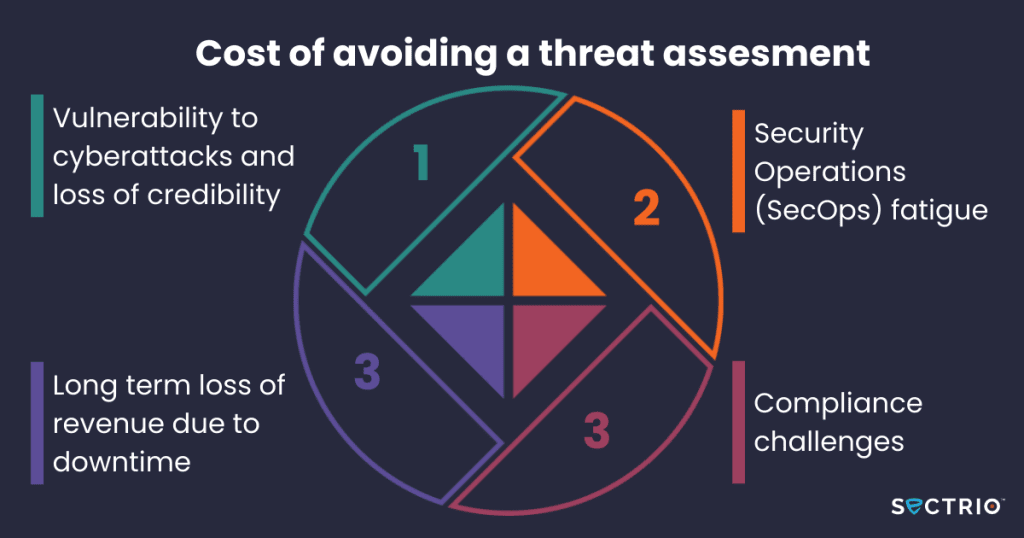
Most businesses are not conducting security audits frequently enough. They are also not investing adequately in ramping up their security posture to cover new and emerging threats. The reason for this is simple. These businesses are not conducting enough threat assessment runs to understand internal and external threats and vulnerabilities they are exposed to. This makes such threats and vulnerabilities invisible to them and these businesses continue operations on a BAU mode while the threats multiply and grow in sophistication and potential impact.
A threat assessment exercise when done in the right way at the right time could save millions in revenue, downtime avoided, and loss of market share due to delays in production and shipment of products.
what are the components of a good threat assessment program?
- Frequency: calendarize the exercise so that the exercise is taken up periodically and frequently
- Coverage: cover the infrastructure as a whole including devices, networks, HMI units, SCADA systems, data platforms, and everything connected. It should also cover access privileges and any and all components including, if possible, assets that are not yet added but will be in the short term
- Methodology and framework: threat assessment should not be aligned to compliance objectives alone. Instead, it should also take into account all operational sources of risk, threat surfaces, and all infrastructure components. The core framework should be flexible enough to incorporate any changes in operations and the methodology should ideally be unique to your business keeping the parameters mentioned above in mind. It is advisable to build a unique methodology and framework for your threat assessment program
- Be clear about the objectives and outcomes. Also, a threat assessment program that doesn’t have an action plan for improving security is as good as a non-existent one
Working with a cyber threat assessment partner like Sectrio can improve the outcomes and shrink the learning curve. Sectrio will build a unique framework and method for you from the ground up and conduct the exercise as well.
Benefits of Sectrio’s threat assessment program:
- Get a comprehensive report on your cybersecurity posture including all threats, risks, vulnerabilities, misconfigurations, exposed threat surfaces, and entry points for threats
- Prioritize top threats so that you can avoid straining your resources while addressing the threats
- Action plan and roadmap to address the challenges and scale to the next level of security
- Rating on how your existing security posture compares with your threat environment
- Impact assessment for key risks, vulnerabilities
- Enhance maturity level of IT operations and improve data security
Try our threat intelligence feeds for free for the next two weeks.

Get access to enriched IoT-focused cyber threat intelligence for free for 15 days
Book a demo now to see our IT, OT, and IoT security solution in action: Request a Demo






